Configuring IBM Verify Identity Access
Configuring IBM Verify Identity Access(IVIA) Web Reverse Proxy
IBM Verify Identity Access (IVIA) Web Reverse Proxy acts as the point of contact for the IBM Verify Identity Access OIDC Provider(IVIAOP).
The minimum version required for the IBM Verify Identity Access OIDC Provider is 10.0.6.0.
The steps below must be followed to configure IVIA:
-
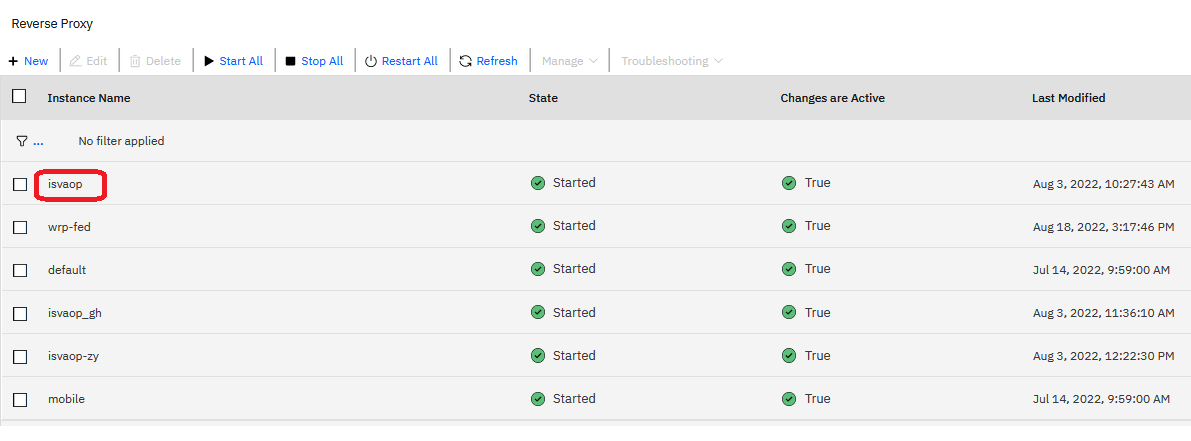
Configure the OAuth and OpenID Connect Provider Configuration, Navigate to Web -> Reverse Proxy, select the reverse proxy the you to configure as point of contact.
-
Navigate to Manage -> AAC and Federation Configuration -> OAuth and OpenID Connect Provider Configuration.

-
Select IVIA OIDC container based provider.

-
Navigate to IBM Verify Identity Access OIDC Provider Runtime tab. Provide the IVIAOP runtime details such as Host name, Port, Junction and the option to Load Certificate. Click on Next.

-
Reuse certificates and Reuse ACLs are selected by default, uncheck them to change the default behavior. Click on Finish.

-
(Recommended) Set
content-security-policyandx-frame-optionsheaders to be restrictive. Navigate toWeb -> Edit Configuration Fileand update the[rsp-header-names]to the desired values. -
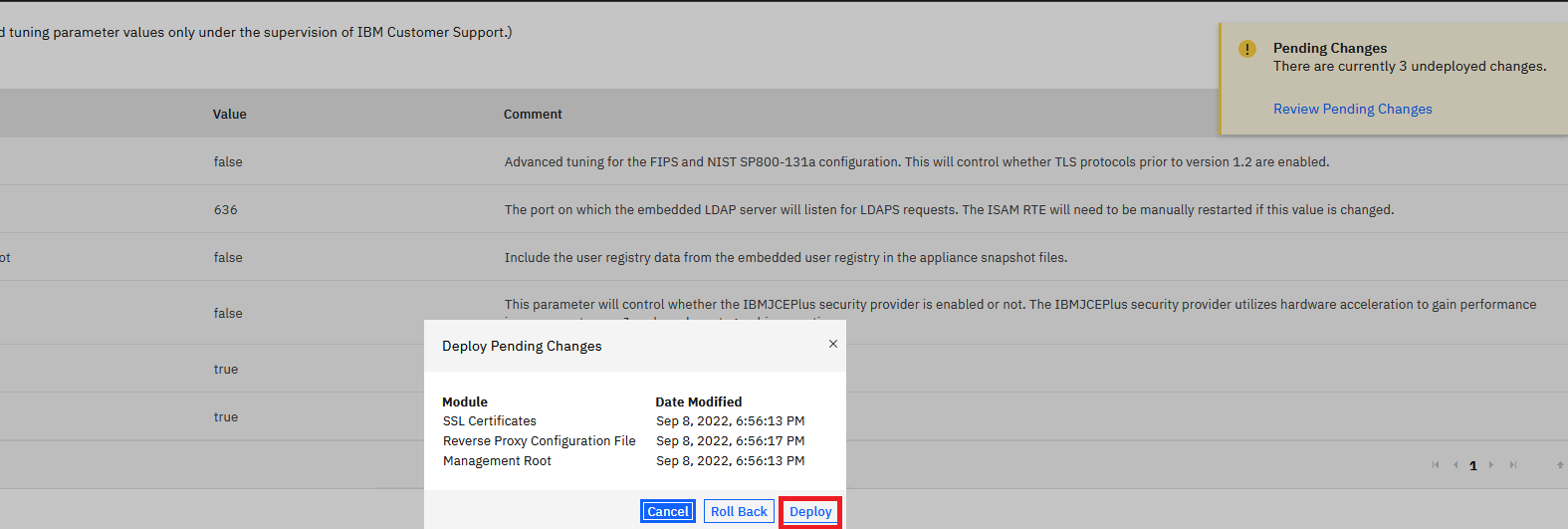
Deploy pending changes and restart reverse proxy. In the case of a container deployment of Verify Identity Access, you will also need to publish the container configuration before restarting the Web Reverse Proxy container.
NoteTo run device flow, set the user_authorize endpoint to anyauth ACL.
- Once this is completed, update the
base_urlin the provider.yml tohttps://<proxy>:<port>/{junction}. This is the point-of-contact URL to access IVIAOP and is used to update the OpenID Connect Discovery Metadata endpoints.
definition:
...
# Other configuration
base_url: https://isvaop.ibm.com:445/{junction} # Base url of the endpoints.Authentication
IBM Verify Identity Access OIDC Provider does not embed an authentication service. It relies on the Web Reverse Proxy (WRP) as a point-of-contact for authentication or directly uses Verify Identity Access Advanced Access Control. In both cases, Verify Identity Access WRP acts as the session manager and is configured to forward session credentials (as a JSON Web Token) to IVIAOP.
The recommended approach is to use the Web Reverse Proxy to mediate and manage authentication.
IVIA Web Reverse Proxy acts as the point of contact IBM Verify Identity Access OIDC Provider, by default. The POC wizard configures an anyauth ACL to the /{junction}/oauth2/auth endpoint. When a specific flow, such as the authorization code grant flow, requires authentication, IVIAOP redirects to this endpoint to initiate user authentication.
No additional configuration is required for this.
Updated 18 days ago
