Pushed authorization request
Introduction
The Pushed Authorization Request (PAR) enables a Client to push the payload of an authorization request directly to the authorization server. A request URI value is received in exchange that is then used in the authorization request through the user agent. The OIDC Provider is able to reference the request based on the request URI.
Typically, in grant flows such as Authorization Code, the request parameters are sent as parameters through the user agent (as URI query parameters). This, while simple, presents some challenges:
- The request is not tamper-proof.
- The request is not confidential. This may be important when sensitive or regulated information might need to be shared in the request.
- Authorization request URLs can become large, particularly when adding additional request context, which might cause processing errors depending on the implementation.
JWT-Secured Authorization Request (JAR) offers a solution to some of these challenges by wrapping the request parameters in a signed and optionally encrypted JSON Web Token (JWT). In order to cope with the URL size restrictions, JAR introduces the request_uri that the OIDC Provider invokes to obtain the request JWT. This can be cumbersome to maintain.
PAR, on the other hand, pre-registers the request parameters and the request_uri contains an identifier generated by the OIDC Provider itself that keys it to the request parameters. The Client must authenticate itself using any of the client authentication methods configured, such as using a client_id/secret or private_key_jwt assertion. This presents a simple mechanism to address the challenges and reject requests early if they fail validation at the OIDC Provider.
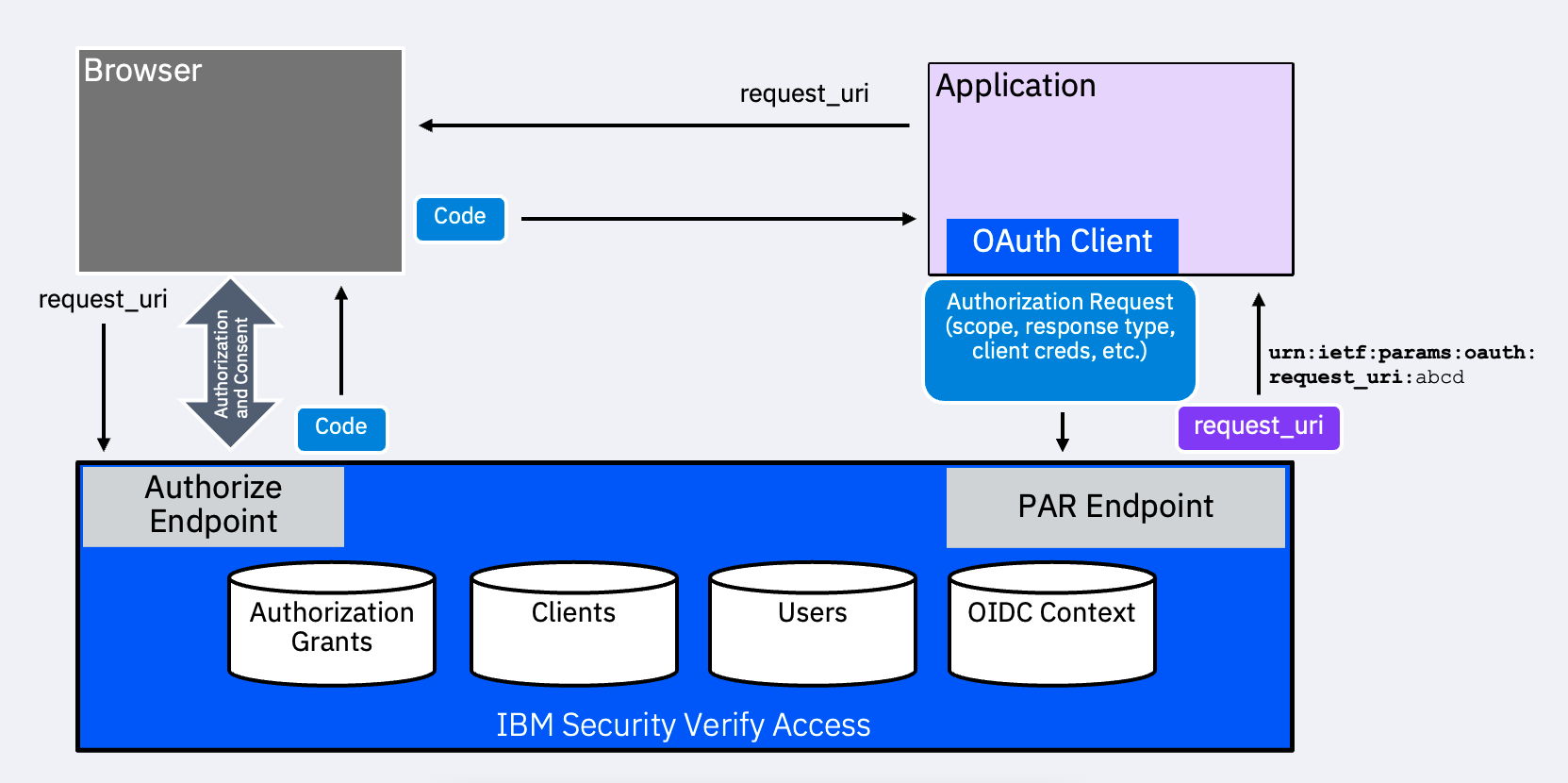
The process of exchanging the code for tokens remains the same as the standard grant flow.
Using the JWT-Secured Authorization Request
The Client may use JAR to push a request object JWT to the PAR endpoint, if an additional level of integrity validation is required. This is required in some regulated standards, such as for some Financial Grade API (FAPI) profiles.
However, the request_uri cannot be used in the PAR payload.
Updated 18 days ago
