Threat Detection and Mitigation
`
Threat Detection and Mitigation
Introduction
IBM Verify SaaS offers native threat detection and remediation, identifying credential stuffing or compromised credential attacks, brute force attacks. For example, Multiple failed logins, login deviation attacks, and actionable IP address that are considered suspicious.
Admins can set their Verify SaaS environment to alert or proactively block or both login traffic that results from identified attacks. The attacks can originate from attacks on your specific IBM Verify SaaS environment. They can also be attacks that are identified from other Verify SaaS tenants in which your tenant can take proactive mitigation.
IBM Verify detects suspicious traffic with indicators of attack to generate a threat event. Admin can review threat events by using Threat Events report, taking manual proactive actions such as blocking a user. This document covers how admins can define threat detection and remediation policy.
Prerequisites
To enable the Threat intelligence feature in the IBM Verify tenant, contact the IBM support. https://www.ibm.com/mysupport/s/topic/0TO500000002XbyGAE/security-verify?language=en_US
Threat Detection and Remediation policy enablement
The document covers how admins can create threat detection and remediation policy and enable it to be evaluated during the first factor login flow. After the Threat detection and remediation policy is created and enabled, it gets evaluated during each login flow, including Cloud directory, W3, or any other login type supported by Verify.
See the following steps for policy configuration and its usage.
- Create the threat detection and remediation policy.
- Enable the threat detection and remediation policy
- Evaluate threat detection and remediation policy during first factor login flow.
Creation of the threat detection and remediation policy
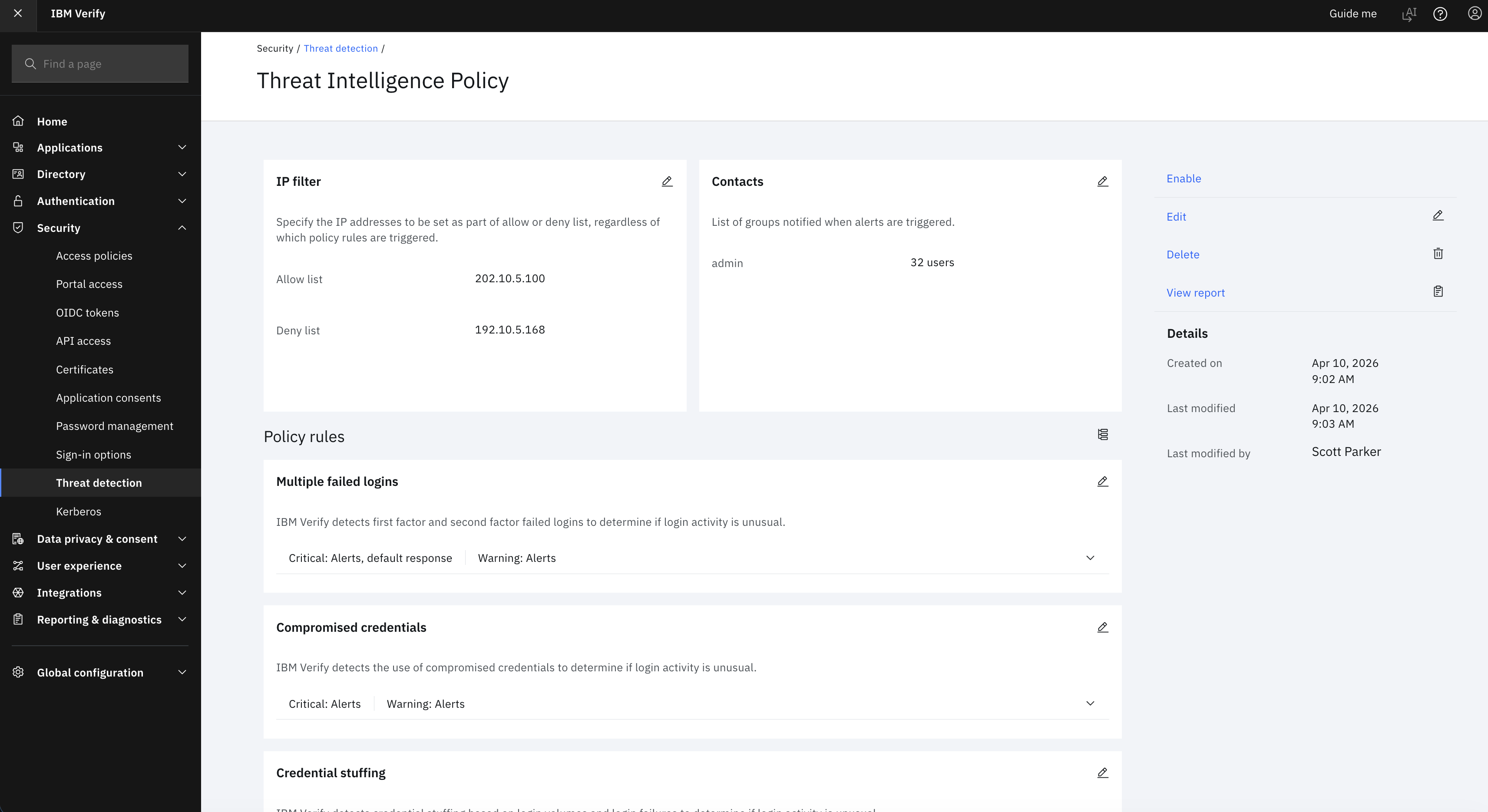
The threat detection and remediation policy contains different types of indicators of attacks. The types are contained in the following list. The administrator can determine the ones to proactively remediate by enabling or disabling threat rules.
- Multiple failed logins
- Use of common credentials – Compromised Credentials
- Credential stuffing
- Login deviations
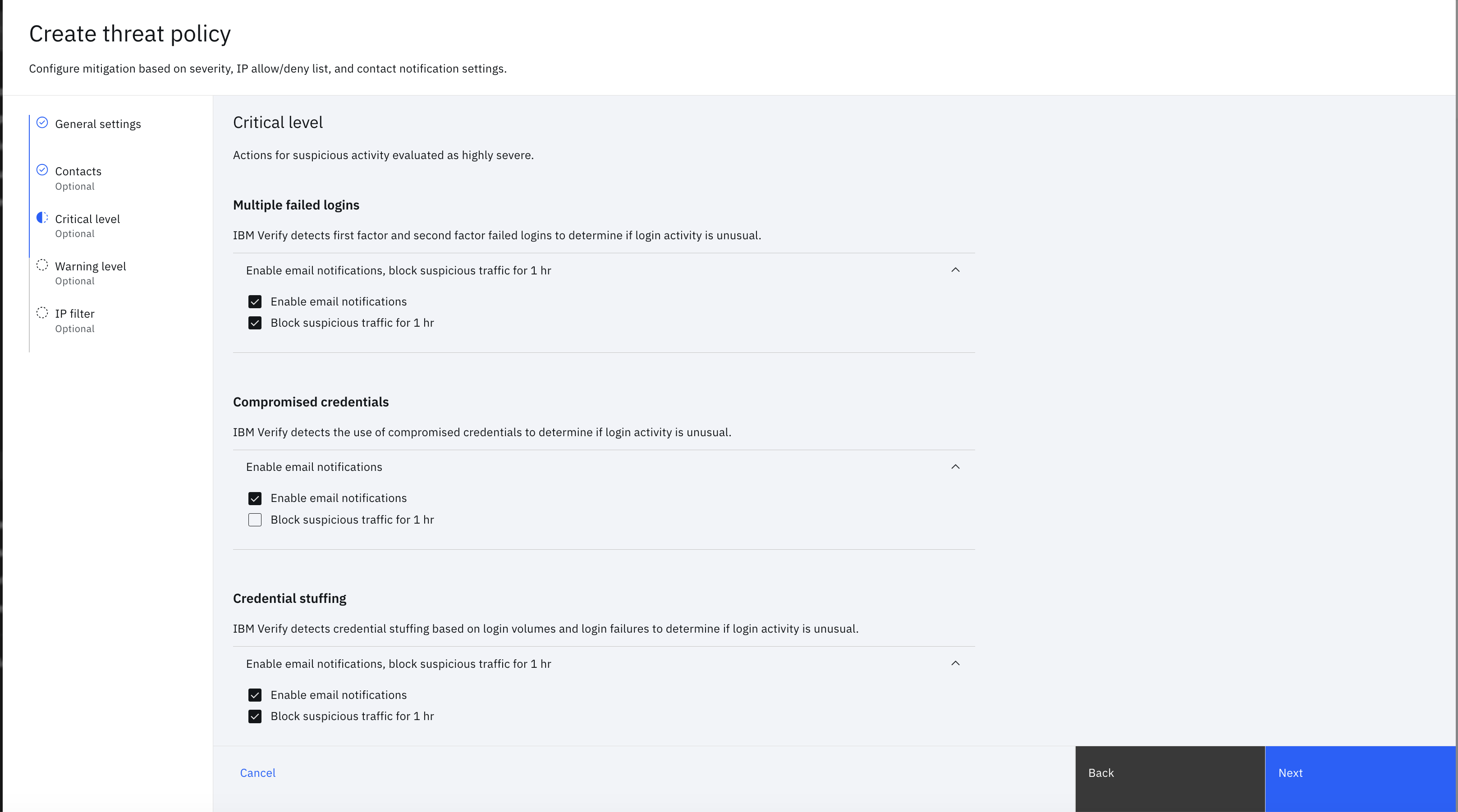
The admin can define the rule actions and alert type for each policy. For example, the suspicious IP address can be blocked for an hour or the admin can receive an alert. Suspicious IPs might be based on indicators of attack that are seen in another tenant as well.
See the following steps for creation of threat policy by using UI.
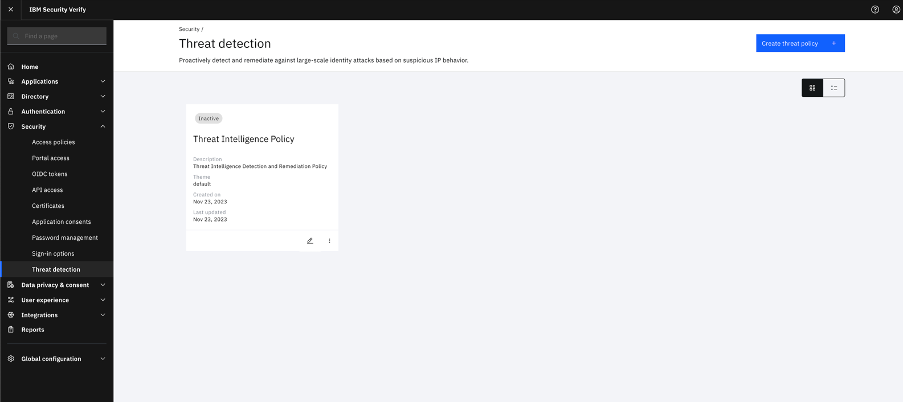
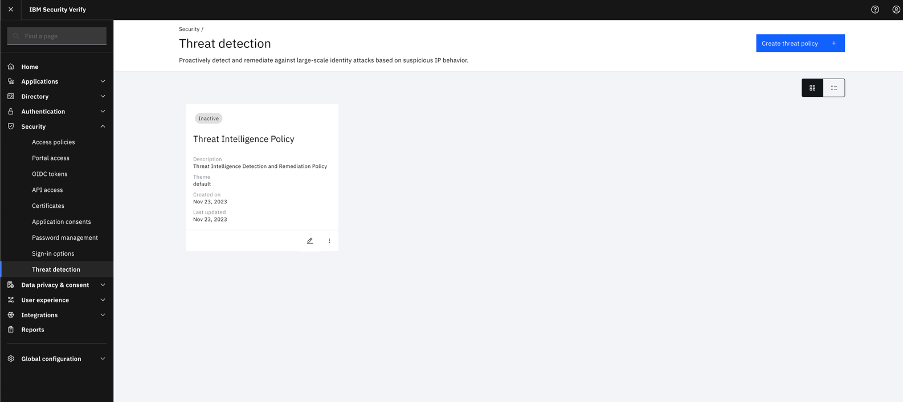
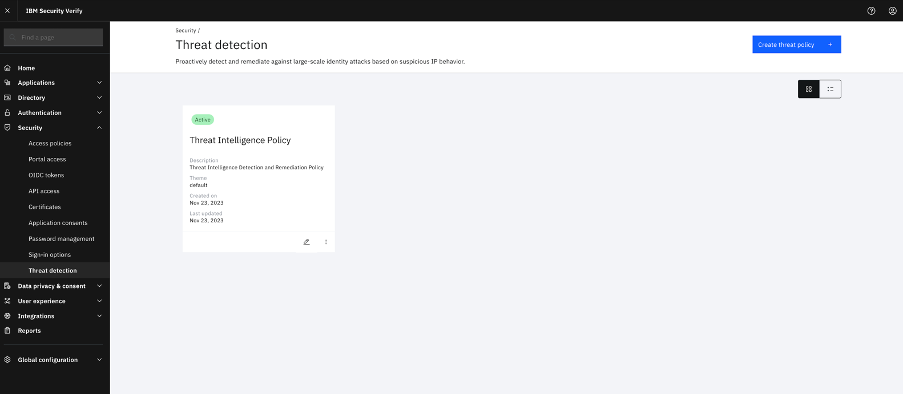
- Log in to Verify tenant as an Admin and click Security -> Threat detection.
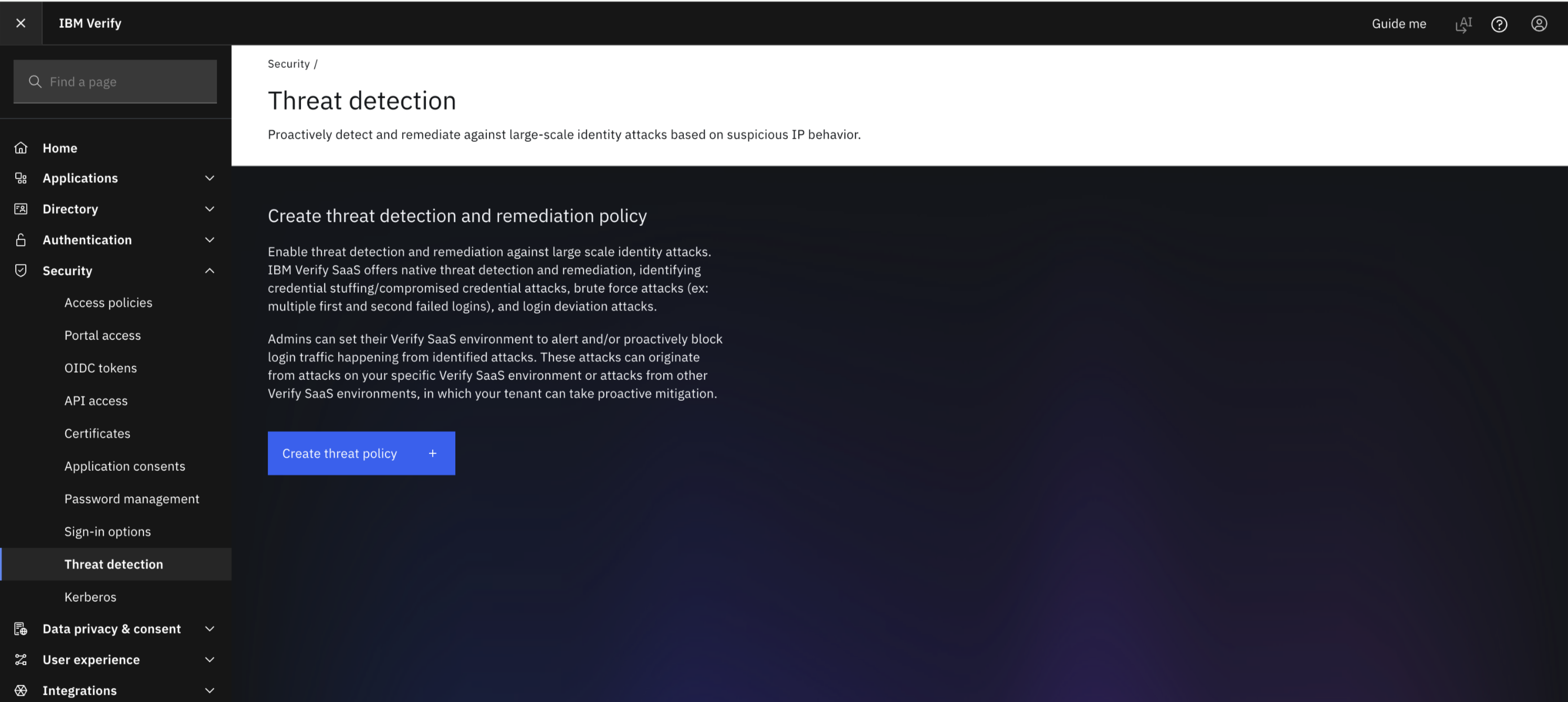
- Click Create threat policy.
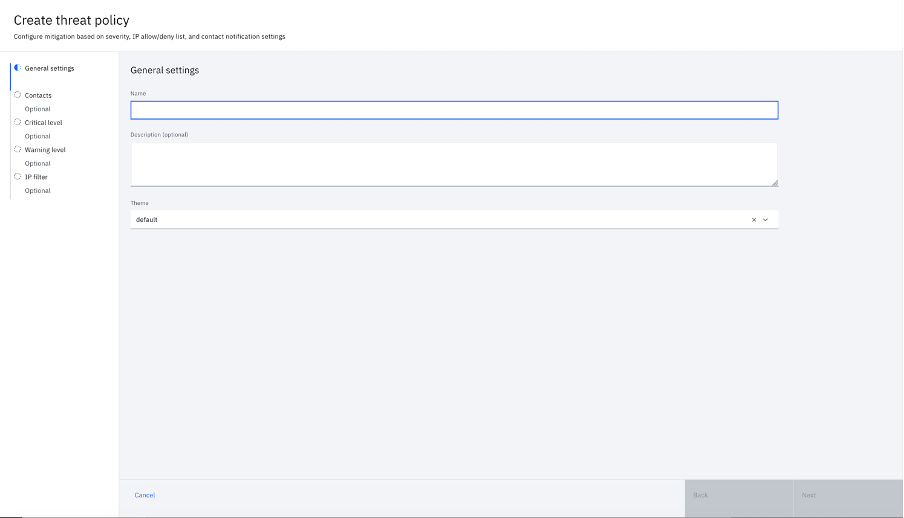
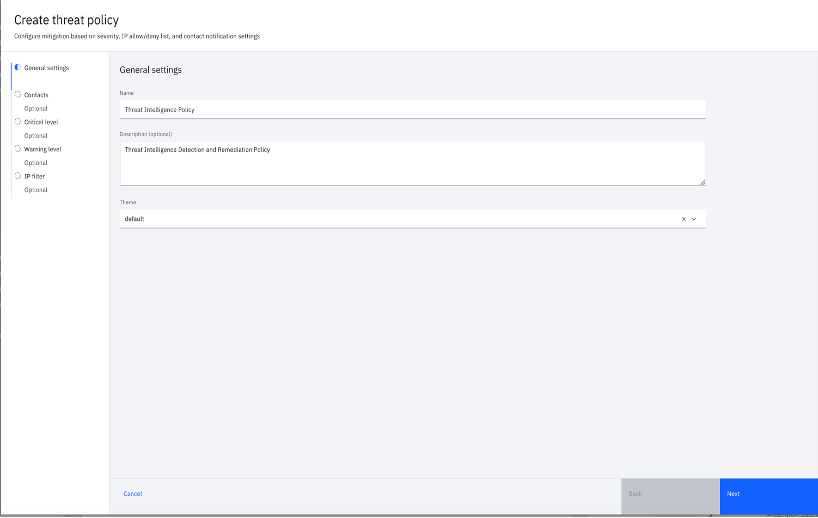
- Specify the threat detection and remediation policy name and description and click Next.
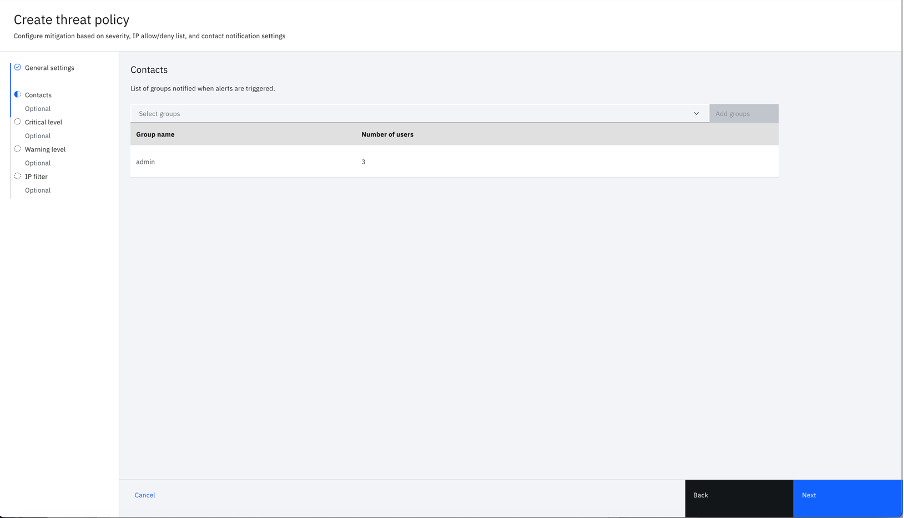
- Under the Contacts section, select the Verify group to be notified during detection flow if the IP is suspicious of any specific Threat policy rule and click Next.
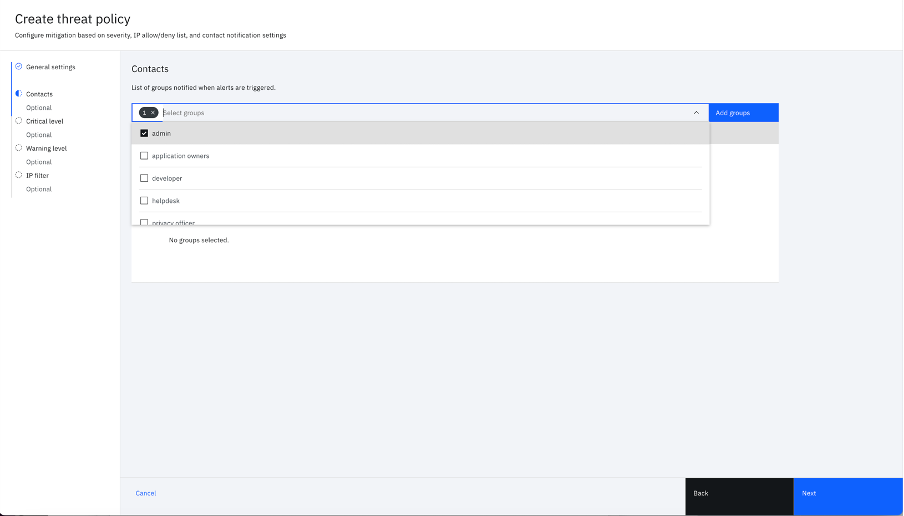
- After the groups are selected, the screen displays the records in tabular format that are listed by Group name and Number of users. Click Next to continue.
- The Critical level section is displayed.
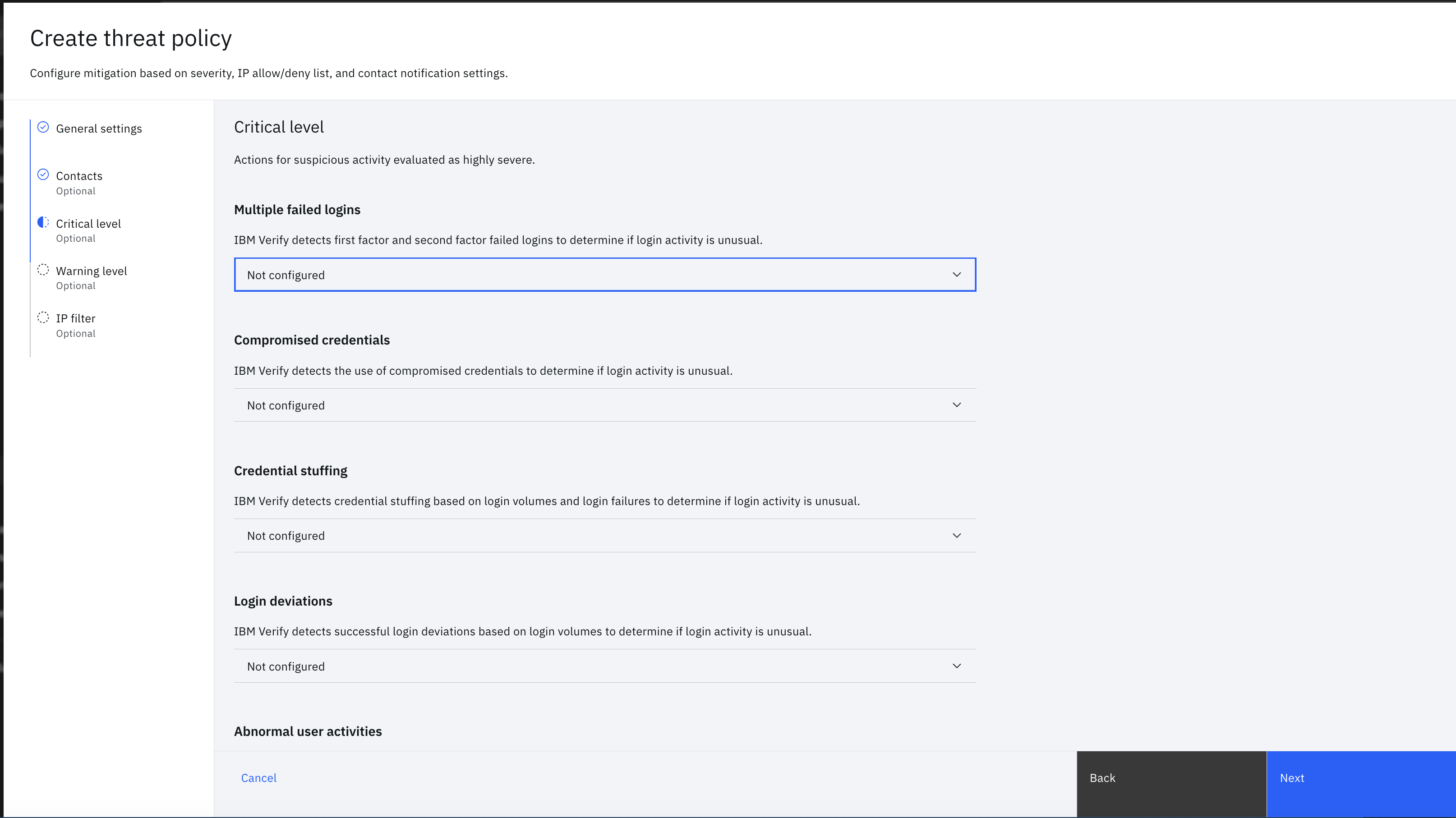
- User can configure critical level setting for each of the rules, either they want to get notified (alerted) or want to block IP for 1 hour, as follows
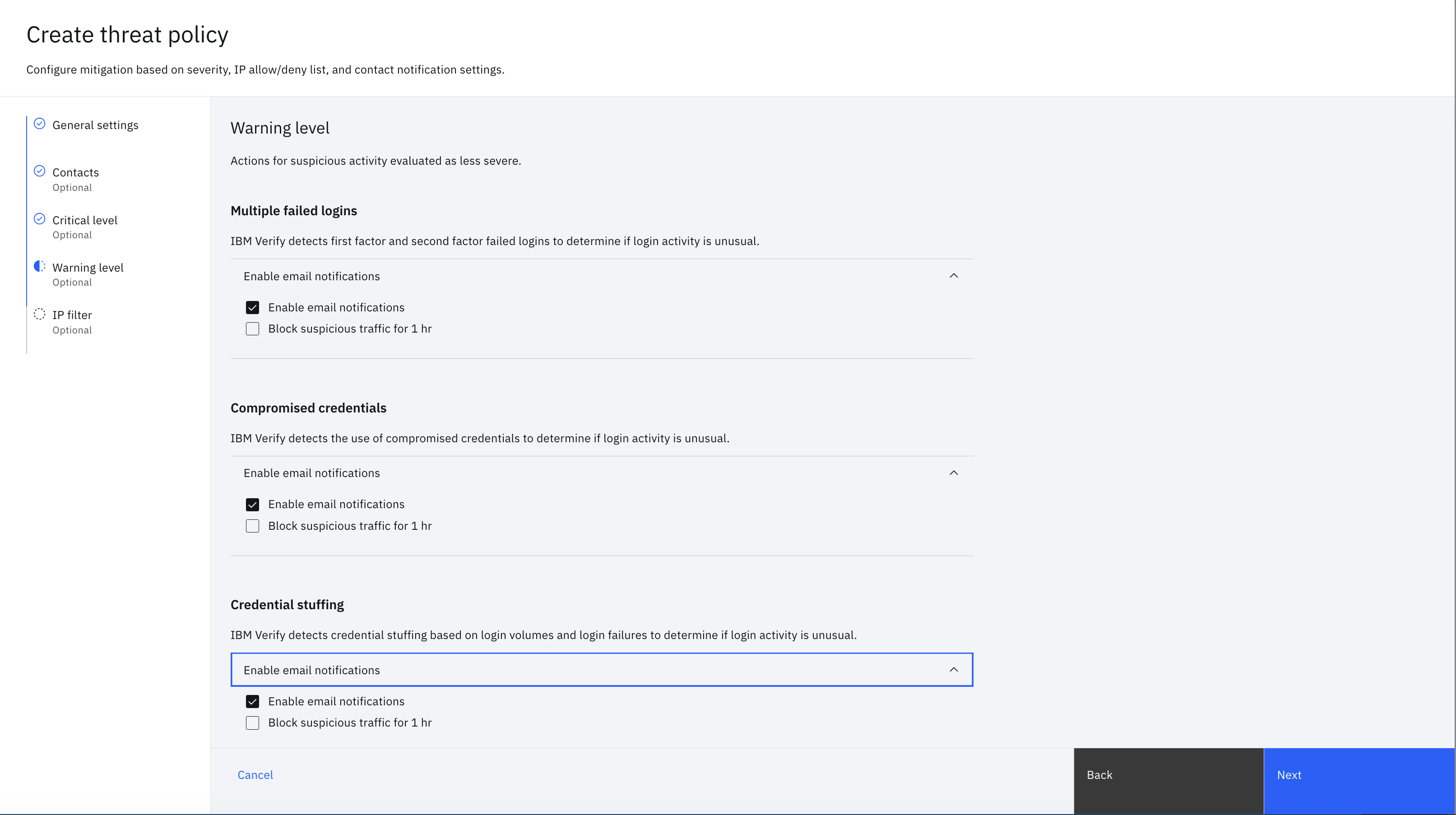
- Click Next to continue. The Warning level section displays settings similar to Critical level as follows
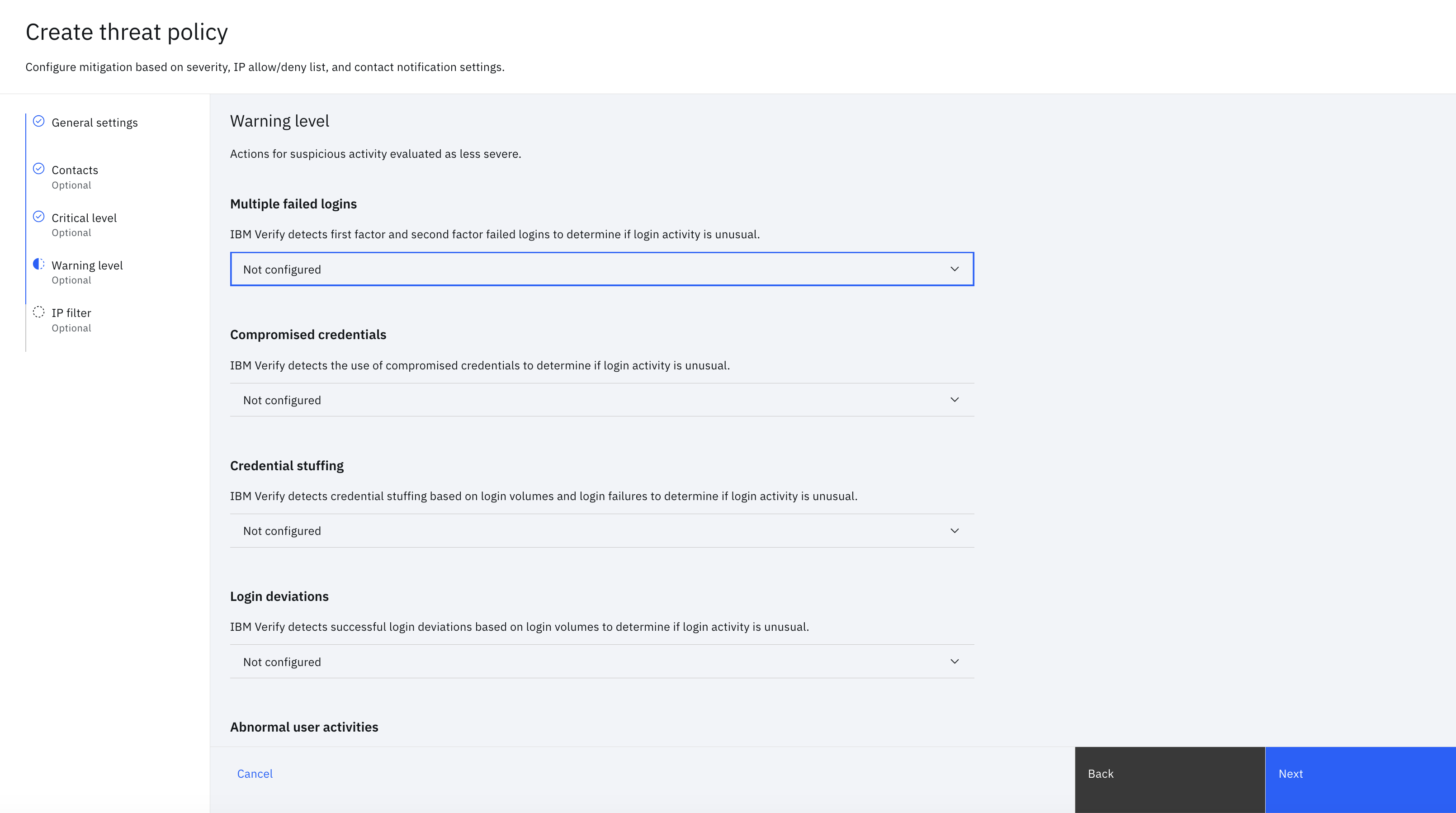
- The user can opt if they want to get alerted or block the suspicious traffic or both or none.
- Click Next to continue. In the IP filter section, the user can include a list of IP addresses to be allowed or denied during each login flow.
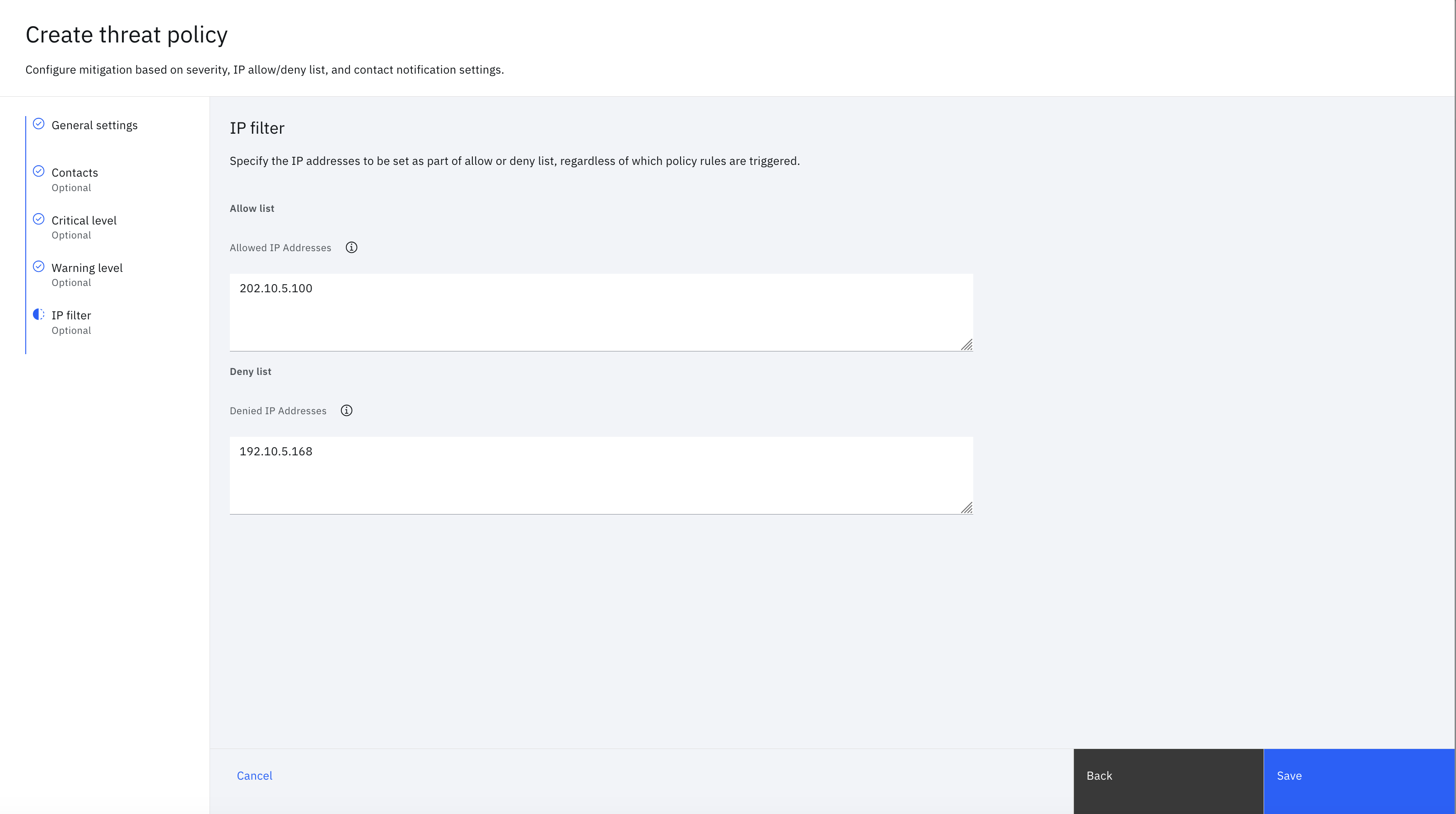
- Click Save to create the threat detection and remediation policy as follows
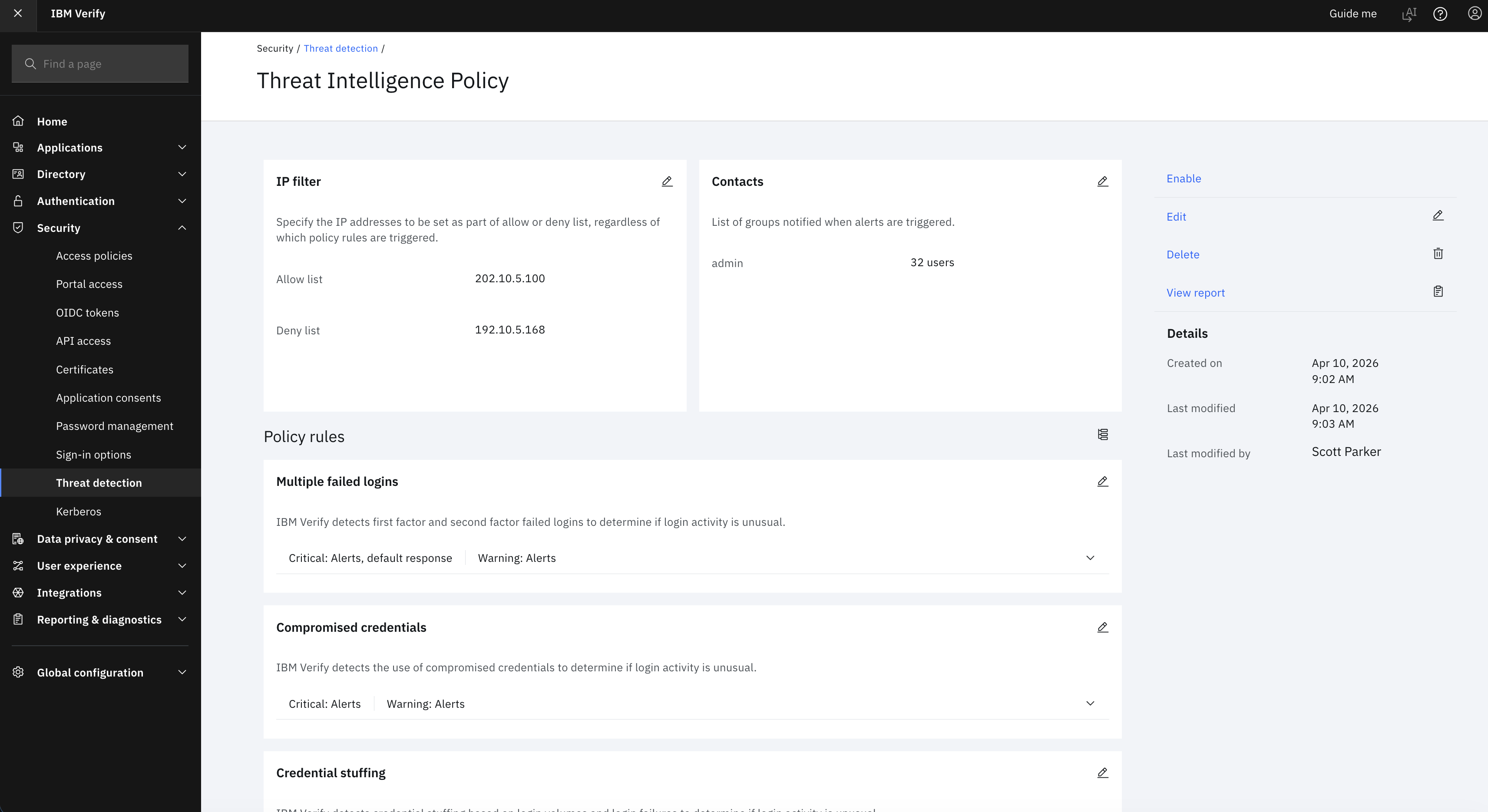
- The threat detection and remediation policy is created.
After the threat detection and remediation policy is created, the next step is to enable this policy for use in the login flow.
Enable Threat detection and remediation policy
- The created threat detection and remediation policy is still not active or enabled. To enable the policy, click Edit.
- The threat policy screen is displayed as follows. Click Enable to activate the policy.
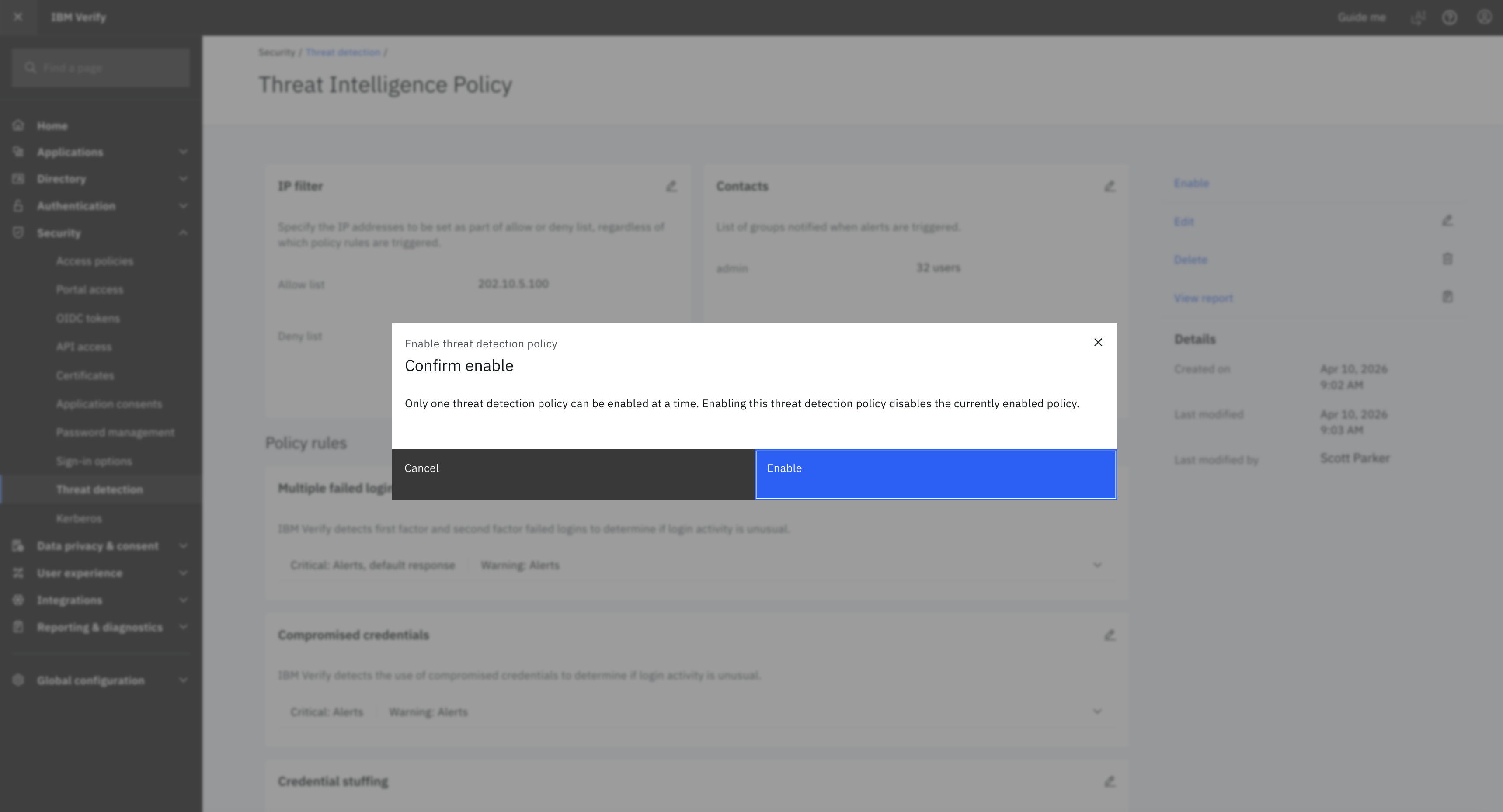
- A confirmation message is displayed as follows
- After the policy is enabled, a confirmation message is displayed as follows
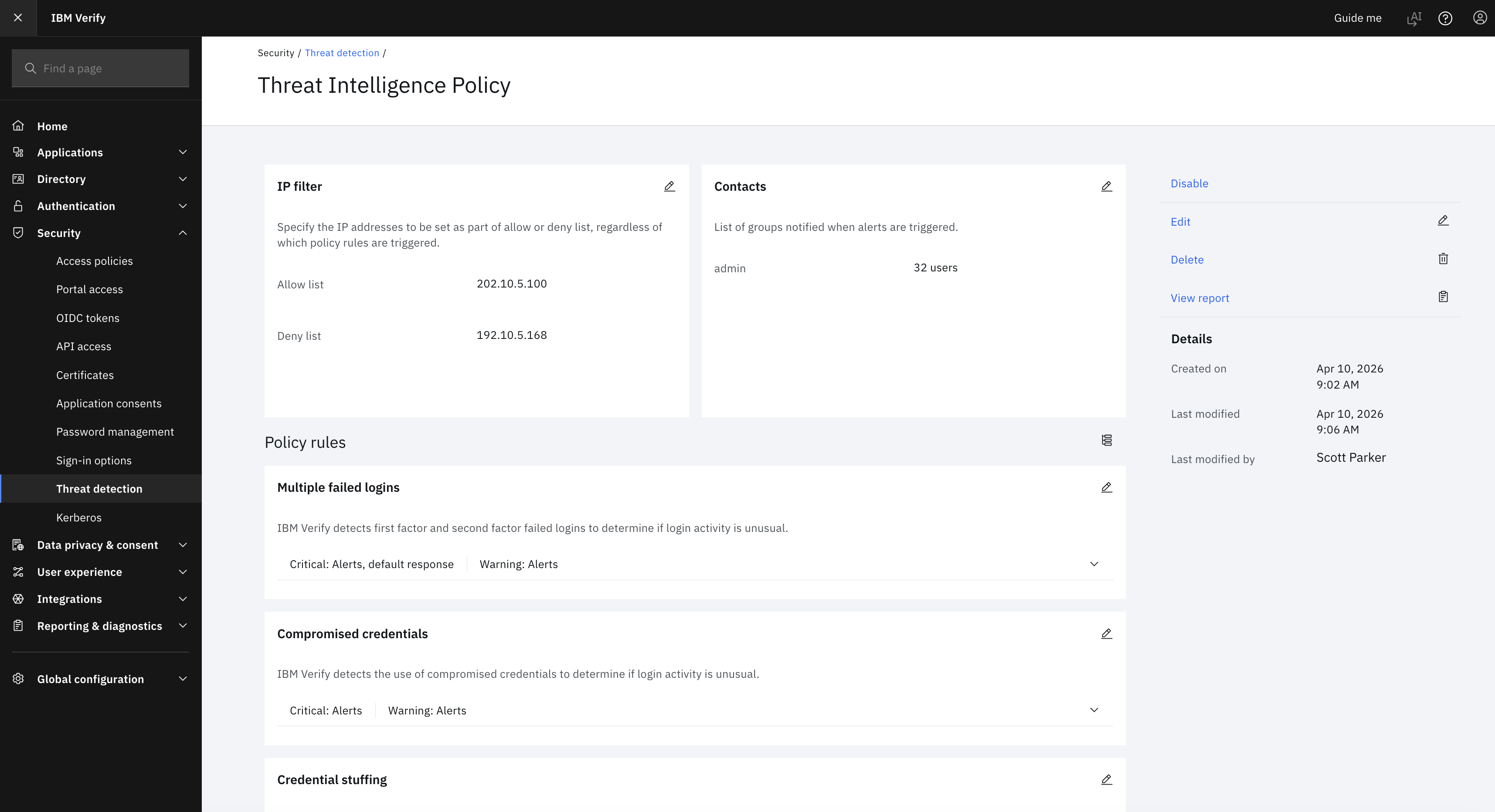
- In the Threat detection screen, the status of the Policy is shown as Active.
During each login flow, the threat detection and remediation policy is evaluated. If rules are configured and a threat is detected, users are alerted.
Evaluate threat detection and remediation policy during first factor login flow
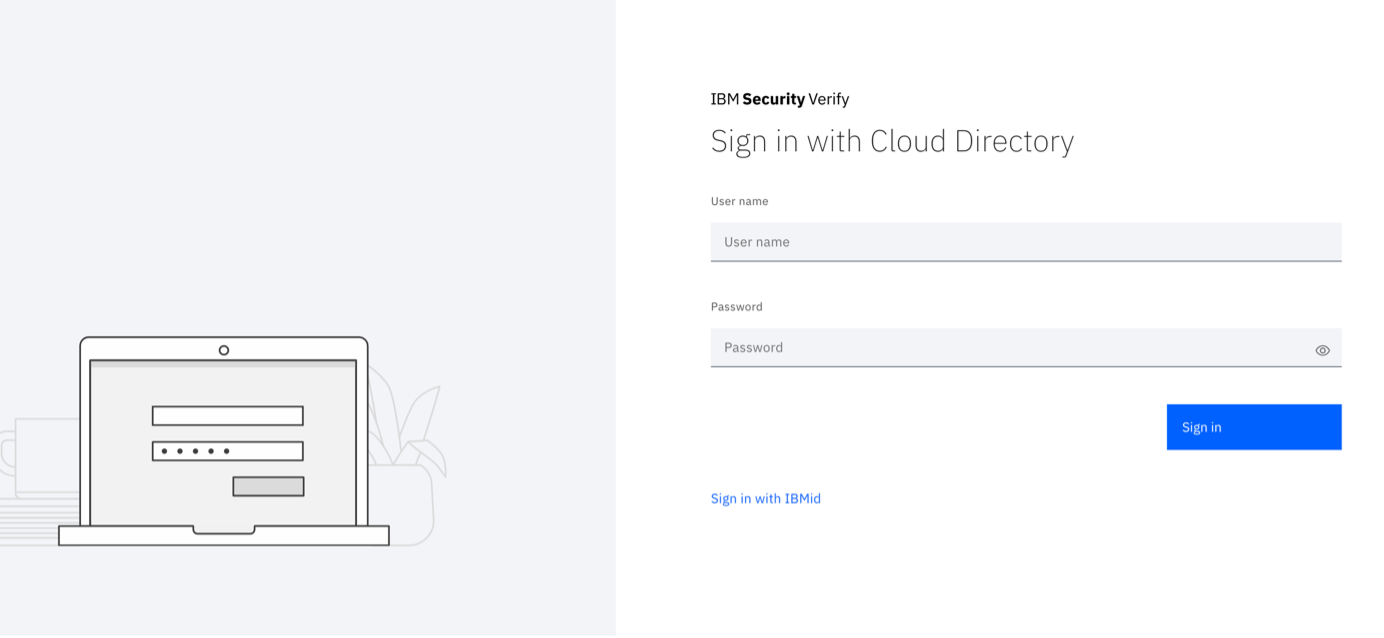
When the threat detection and remediation policy is enabled, the policy is evaluated during each login flow. Log in to Verify tenant by using CD, IBMid, or any other supported login. The threat detection and remediation policy is evaluated during the login flow.
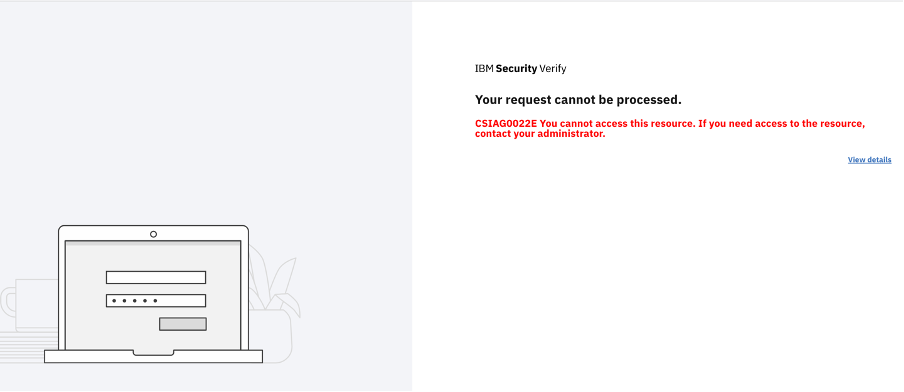
If the source device IP is suspicious according to threat detection and remediation policy evaluation, the user is either blocked or allowed to log in.
If blocked, the following screen is displayed.
- If the IP is not suspicious, then the user is prompted with the login page and allowed to continue.
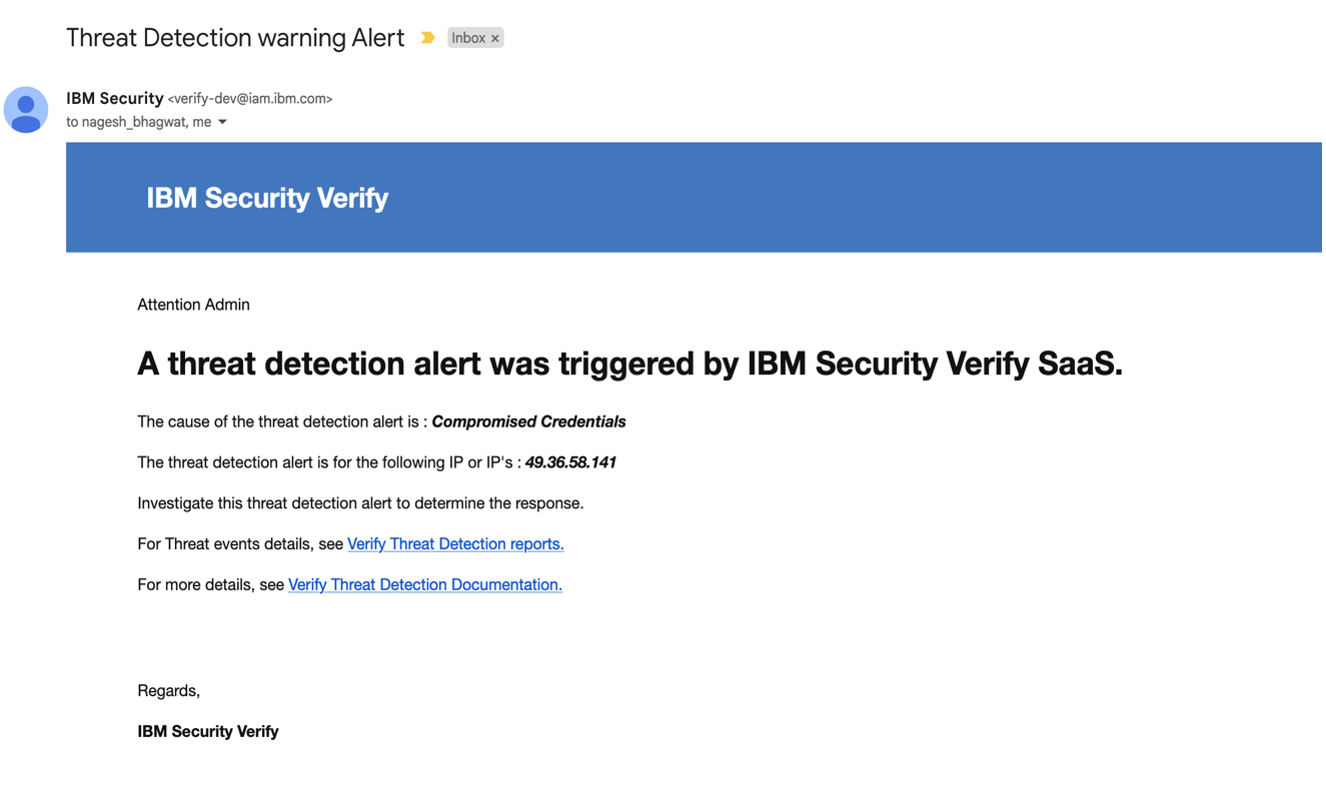
- If the notification is set for any threat detection and remediation policy rule,
- The Verify groups that are selected in the threat detection and remediation policy configuration are able to receive the notification.
- The group members are sent an email message during threat detection.
Conclusion
In IBM Verify SaaS with an enabled threat detection policy, admins can set environments to proactively block login traffic that results from identified attacks and send alert notifications to the admin during such attacks.
- To proactively block login traffic that results from identified attacks and
- Notification alert are sent to the admin during such attacks.
Priti Patil & Nagesh Bhagwat, IBM Security
Updated 25 days ago
