Protect on-premise apps
Did you know that coinciding with the release of the v10.0 of IBM Verify Access (Formerly IBM Security Access Manager - ISAM), you can now use the IBM Application Gateway as a lightweight alternative reverse proxy deployment?
What is the IBM Application Gateway?
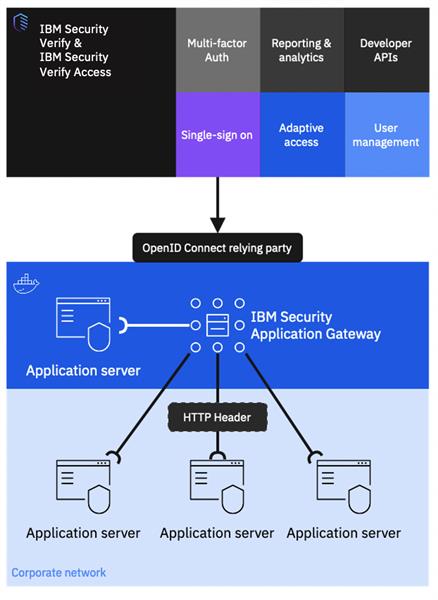
Figure 1. High Level Overview
The IBM Application Gateway (IAG), is a lightweight containerized Reverse Proxy, built with the foundations of the IBM Verify Access, that can be deployed in minutes, with no dependencies. Use the IAG to protect applications traditionally junctioned behind Reverse Proxies without the complexity.
It allows the deployment and protection of a reverse proxy in front of traditional enterprise/legacy applications that do not support modern federation protocols, and depend on standard Single Sign on methods over proxied requests (HTTP Header, JWT, IV-Cred etc). Most of the existing Verify Access/ISAM SSO integrations work with the IAG!
Architecturally, the deployment is simple, where you might have used what was the WebSEAL reverse proxy, you can now use the IAG. It can operate in a loosely coupled arrangement with the centralised enterprise identity provider, under an entirely different SLA. The rich authentication experiences offered by Advanced Access Control (AAC) or Adaptive Access can still be equally viable, and it can be supercharged when deployed in conjunction with OpenShift and Kubernetes to allow for a fully automated deployment experience.
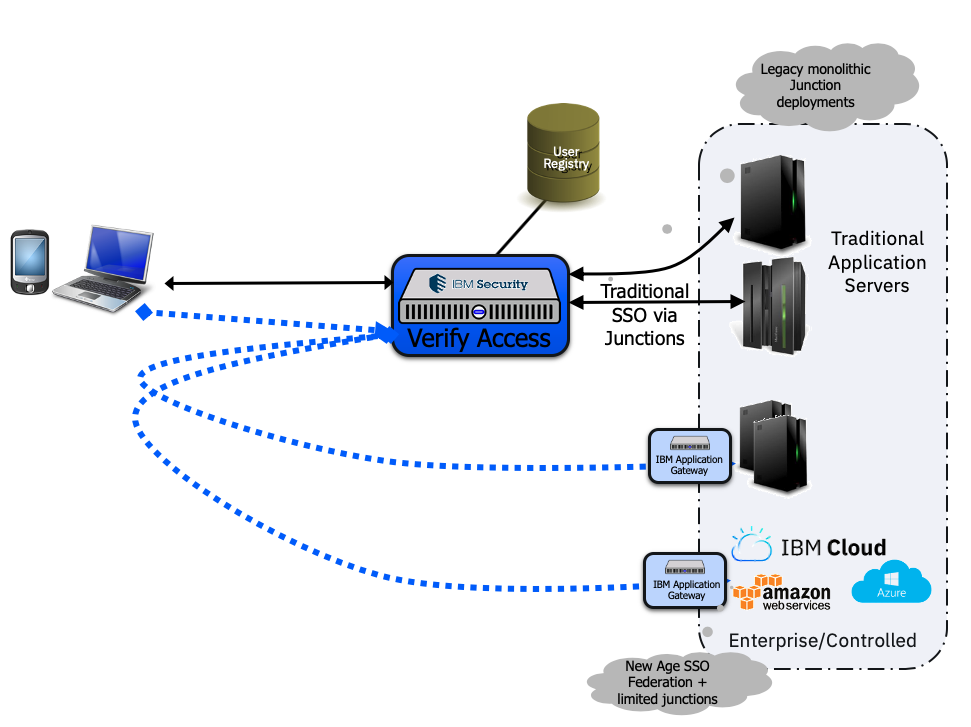
Figure 2. A Hub and Spoke architecture, using IBM Verify Access, in conjunction with the IBM Application Gateway.
The IAG has an inbuilt OpenID Connect Relying Party that can be configured against either IBM Verify or IBM Verify Access to perform the rich authentication experience and allow for the operation of the reverse proxy outside of the centralised enterprise authentication service.
Configuration of the IAG is so simple, application owners can take over the management and lifecycle of the reverse proxy, no longer needing the burden of operations to fall on the IAM administrators. Employing a configuration experience based on files, the deployment states can be easily backed up using source control, and can be easily repeated in each environment.
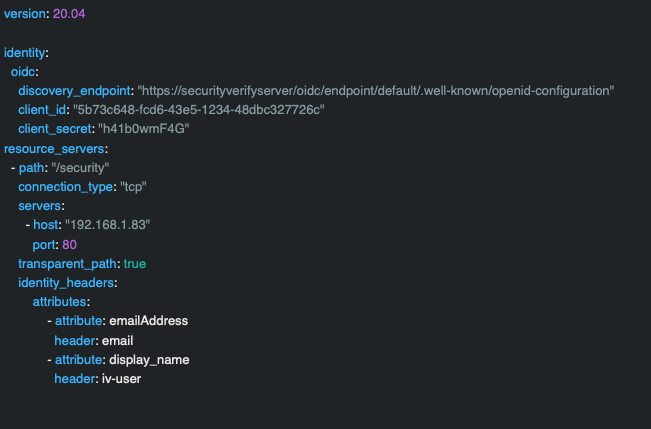
Figure 3. Here is a complete/working example of the configuration required to have the IBM Application Gateway authenticate and single sign into a protected application using a HTTP Header based SSO integration.
Using the developer portal experiences available on both IBM Verify and Verify Access, on-boarding applications can be an almost no contact experience for administrators!
Would you like to know more?Try it out today on Docker Hub
Updated 14 days ago
