Consumer identity
Capture consumer information
Provide seamless and privacy transparent experiences to onboard new users as they register and interact with your brand. This includes ensuring the relationship with consumers is trusted through branded experiences that also allow for verifying consumer information as it is entered. Streamline consumer onboarding with a single, scalable, and secure directory through defining custom attributes that are important to the brand.
Line of business, marketing personas, or others can create registration forms in minutes through a highly customizable GUI to drag and drop the sequence and appropriate fields needed to capture consumer information upon registration. This also ties to data consent, privacy, and terms and condition experience for consumers as they interact with brands. Brands can have a single common registration experience or create multiple registration experiences with specific sub-brand branding and customization, all feeding into a singular view of the consumer.
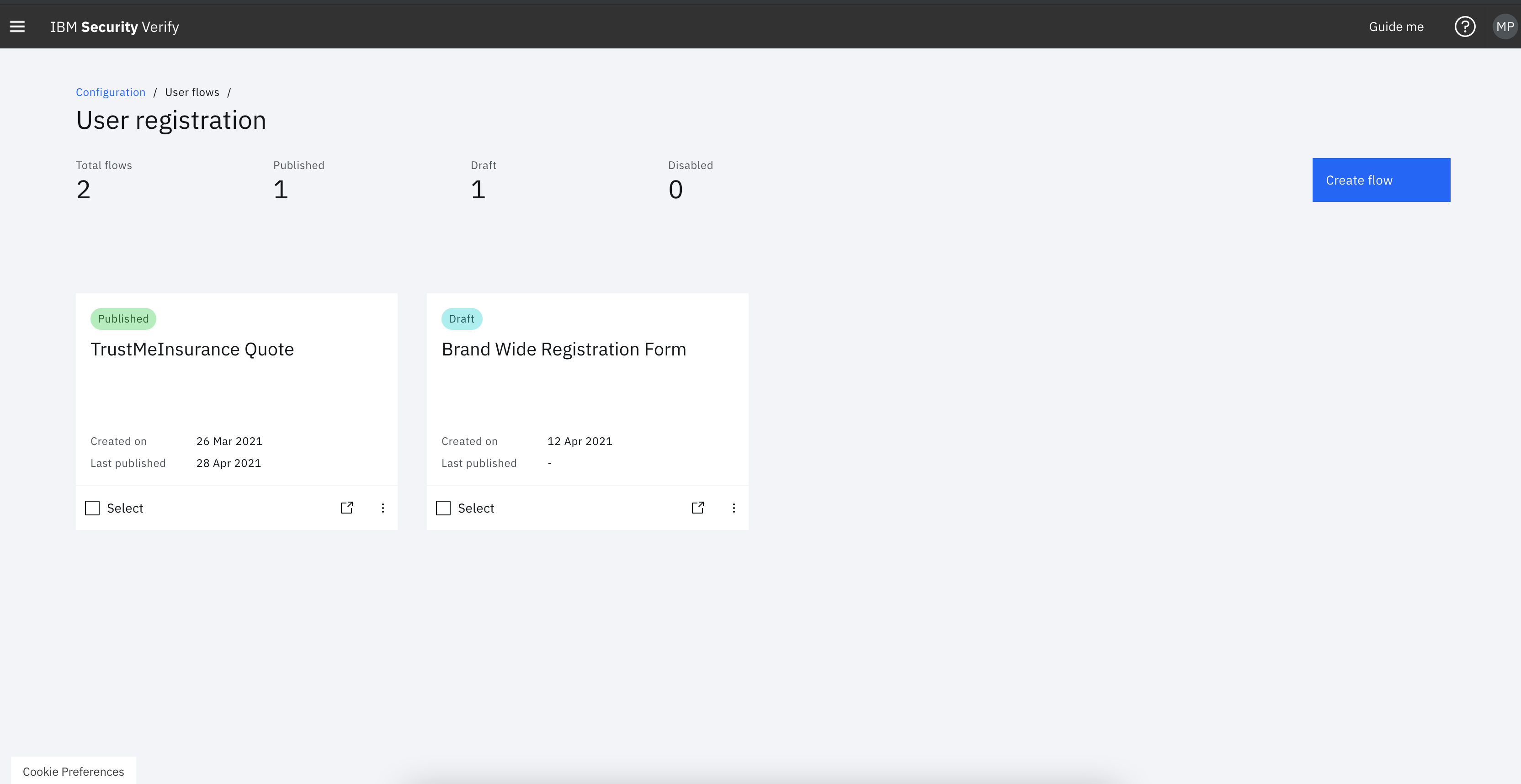
User registration page flow creation, allowing for multiple registration forms to be live and active all funneling to a single view of the consumer
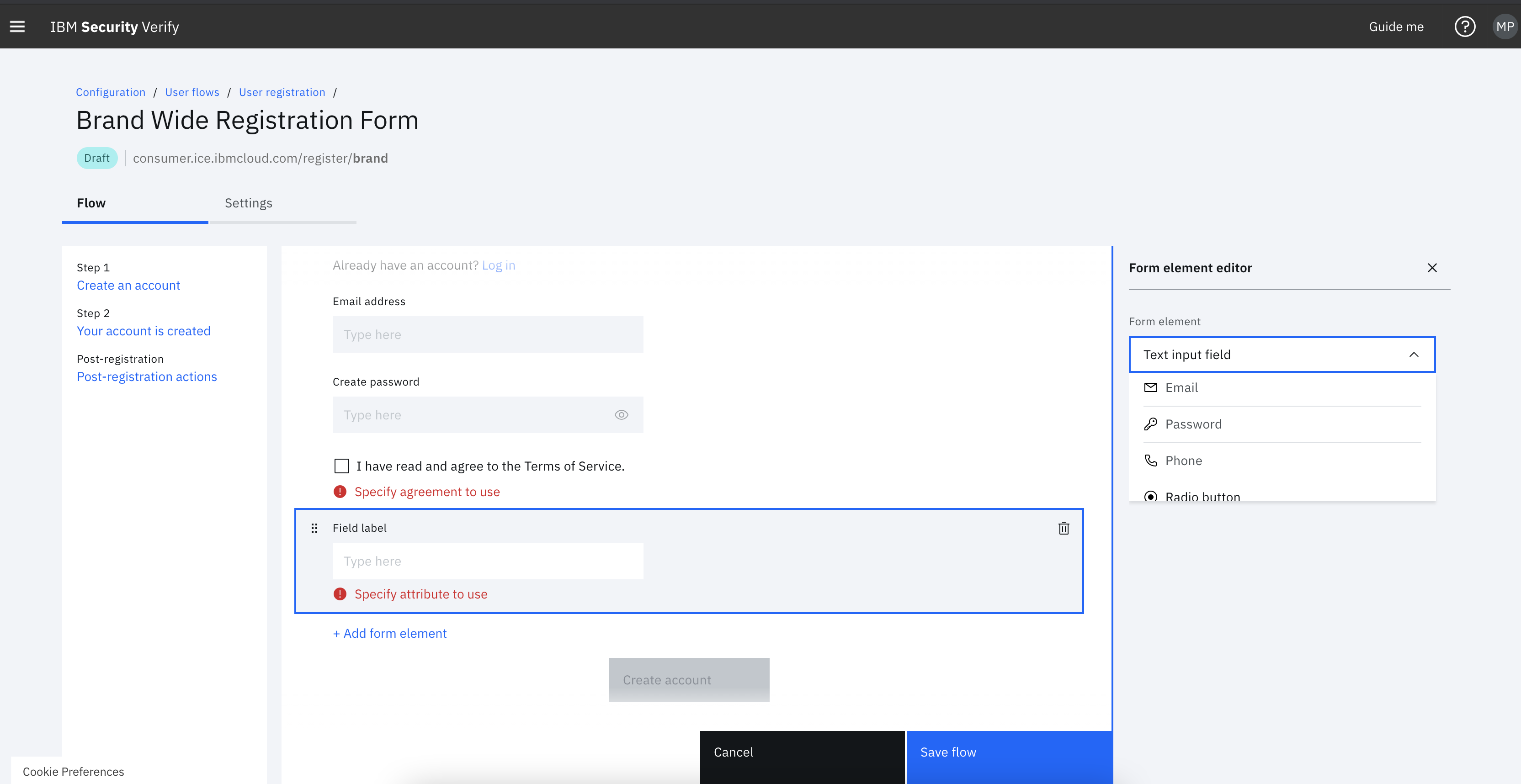
No-code, drag and drop registration form builder to define the sequence, fields, and page navigation.
Engage with consumers
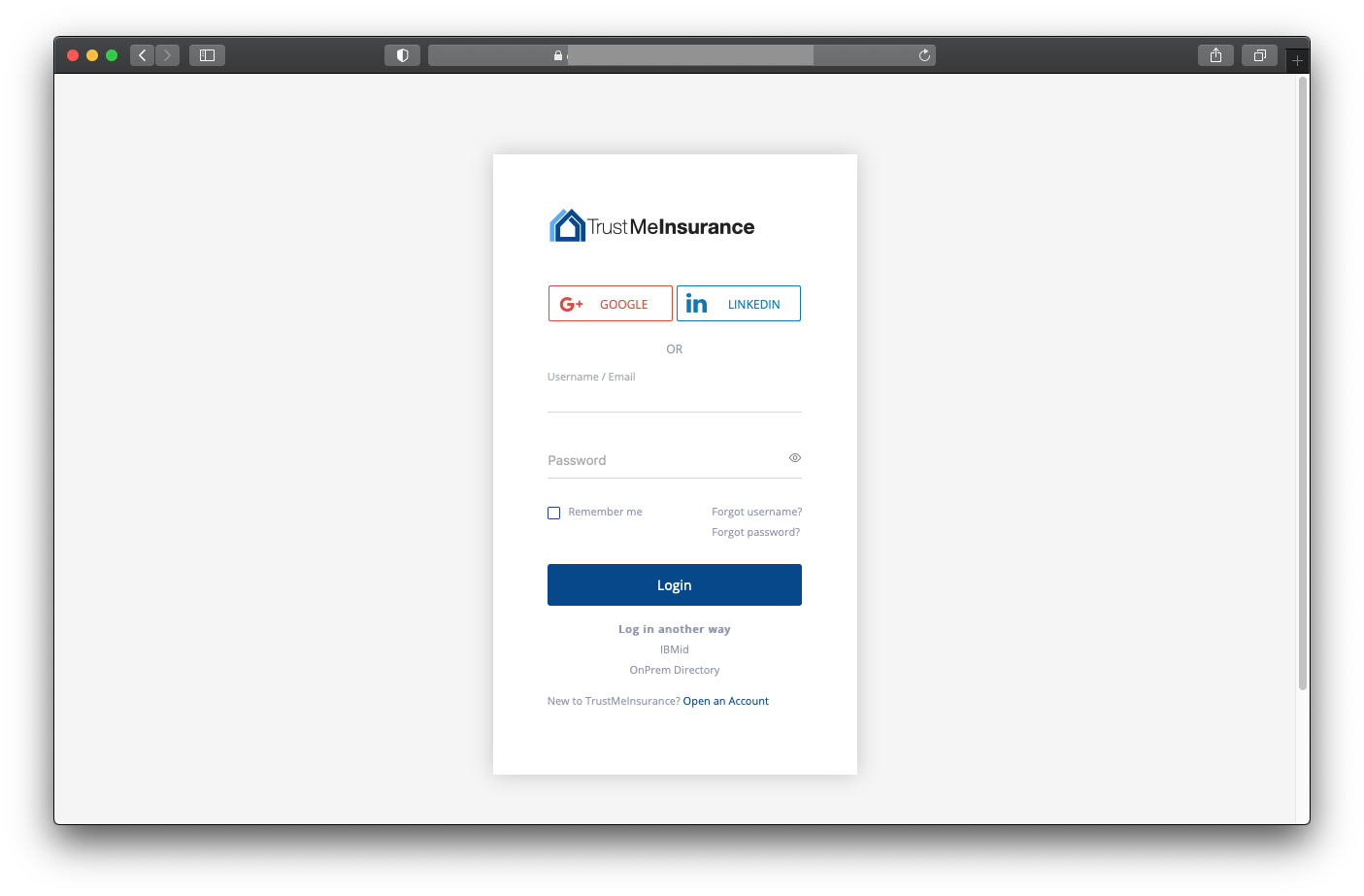
Provide seamless SSO experience that also allows consumers to leverage social logins to simplify how consumer interact with your brand. Enable consumers to determine what MFA types can be used and how they can easily configure them to security engage with brands.
Allow consumers to manage profiles
Provide a self-service experience for consumers to manage their profile settings. This includes modifying profile information, controlling data consents/permissions for opt-in/opt-out preferences, enrolling/de-enrolling MFA methods, and more.
Administer application environments through a scalable platform
Configure the organizations environment to ensure compliance and proper security posture. This entails being able to connect to the proper identity sources, on or off premises. Out of the box analytics and reports allow brand owners to know how consumers are engaging with their applications.
Developer time to value
Hosted registration and profile forms allow developers and application owners to simple configure the forms by dragging and dropping attributes through "low code/no-code" experiences. Developers can customize and brand web and mobile experiences through SDKs to streamline the development process. As backend systems are integrated, like identity sources and user repositories, developers can use standard configuration protocols by simply entering endpoint and secret information, limiting the need to write integration code.
Updated 23 days ago
